Expertise

Blog
Mirror Trading, Wash Trading, and Insider Trading: The Good, the Bad, and the Ugly of Trade Surveillance
Compliance

Financial markets generate enormous volumes of data. Orders, trades, cancellations, price movements, and counterparties all leave traces that surveillance systems monitor continuously. Yet market abuse rarely appears obvious in that data.
In most cases, suspicious behaviour looks almost indistinguishable from legitimate trading. Transactions clear normally, positions balance, and prices move in ways that appear plausible. What differentiates legitimate activity from abuse is not the trade itself, but the intent behind it, contextual clues, and the relationships between transactions.
For trade surveillance teams, that creates a persistent challenge. Detecting abuse requires more than identifying unusual transactions. It requires understanding behavioural patterns across accounts, entities, and time.
Three well-known typologies illustrate this challenge clearly: mirror trading, wash trading, and insider trading. Each represents a different type of detection problem, and each requires a different surveillance approach.
Mirror Trading: When Legitimate Activity Becomes a Risk Signal
Mirror trading, by itself, is not illegal. The concept is simple, investors replicate the trades or strategies of other accounts within their own, typically of more experienced traders and in the same instrument and size. This practice is widely used in legitimate portfolio management and institutional trading strategies.
Asset managers replicate trades across client portfolios. Trading desks mirror positions across related strategies. Prime brokers execute mirrored transactions for clients operating in different jurisdictions. These legitimate uses mean mirror trading activity appears frequently in market data and does not usually indicate misconduct.
The risk arises when mirror trades are used for purposes unrelated to investment strategy. In these cases, the transactions exist primarily to move value between accounts, jurisdictions, or currencies while masking the underlying transfer.
One widely cited example involved clients executing offsetting trades in Russian equities in different markets. Securities were purchased in Moscow in roubles and simultaneously sold in London in dollars. Individually, the trades appeared routine. Together, they enabled the movement of billions of dollars out of Russia while obscuring the economic intent of the transactions.
This illustrates the core surveillance challenge. The suspicious behaviour is not visible in a single trade. It becomes apparent only when multiple transactions are analysed together. Effective monitoring requires the ability to link transactions across accounts and entities, identify offsetting trades executed in different markets or currencies, and evaluate whether the economic rationale of mirrored transactions is plausible.
Wash Trading: Manufacturing Market Activity
Unlike mirror trading, wash trading is explicitly illegal. The practice involves executing transactions where a financial instrument is simultaneously bought and sold. The same party, or coordinated parties, essentially trades with themselves to create the illusion of market activity.
Artificial volume can influence price signals, attract investor attention, or manipulate trading metrics used by market participants. In its simplest form, wash trading is easy to identify, as buy and sell orders are placed simultaneously, however, sophisticated actors rarely operate with such obvious methods.
Modern wash trading schemes often employ more advanced strategies: multiple accounts or intermediaries, slightly varied order sizes or execution timing, trading across related instruments or venues, or coordinated activity among several participants. In isolation each transaction may appear legitimate, obfuscating illicit activity.
For surveillance teams, the key task is identifying the transaction patterns that suggest these collusive trading practices. In the simplest terms, these illicit networks can take various shapes, including ring, star, or tree topologies designed to distribute activity.
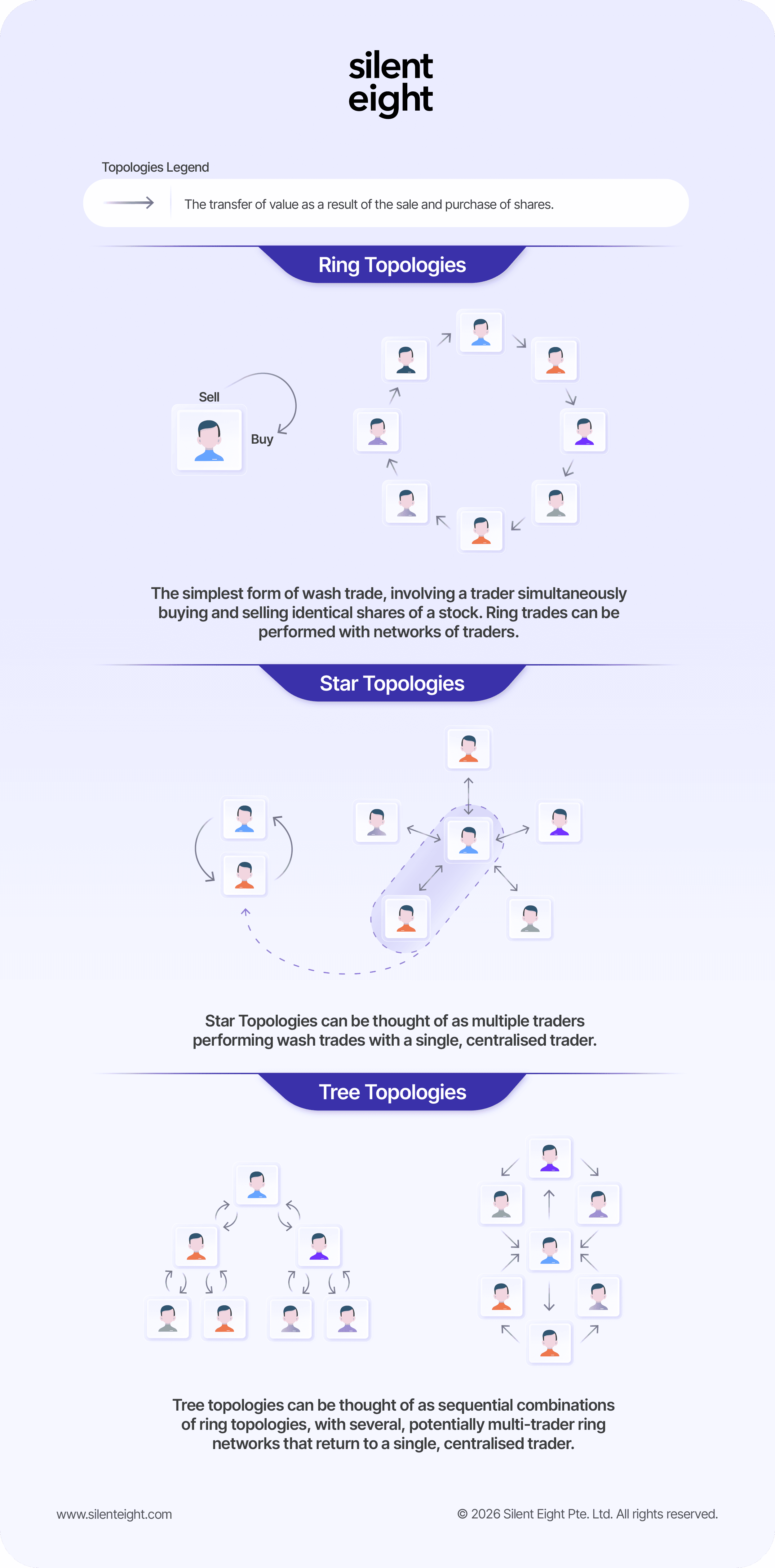
Suspicious behaviour may appear as repeated trades with nearly identical volumes, or sequences of trades that leave all participants with no meaningful net position tend to indicate manipulation.
Crucially, these patterns require surveillance models that evaluate behaviour across multiple transactions and relationships, rather than relying solely on single-trade indicators.
Insider Trading: The Challenge of Detecting Intent
Insider trading presents a fundamentally different detection problem. The activity itself is straightforward: trading securities informed by the possession of market-altering non-public information. In most cases, the transactions themselves look entirely legitimate. For example, a trader purchasing shares before a takeover announcement, or building options positions ahead of an earnings release. On their own, these trades may not appear unusual. The difficulty lies in proving that the trader actually had access to that information. Patrick Kirwin, Head of Product Management at Silent Eight, has this to say:
“The line between intent and coincidence is difficult to judge. Did the person make this particular trade at this particular time by coincidence, or was it their intention to take these actions in an attempt to manipulate the market? [...] Finding markers within trading behavior that can be used to detect and evaluate malicious intent is a key challenge in trade surveillance.”
Red flags tend only to emerge when trading activity is analysed relative to information timelines. Surveillance systems typically look for indicators such as unusual trading volumes before market-moving announcements, profitable options activity shortly before corporate events, and concentrated trading by accounts with historical access to sensitive information.
However, detecting abnormal trading patterns is only the first step. The real challenge begins when investigators attempt to answer key questions: who had access to the information, when they obtained it, whether their trading behaviour aligns with that access, and whether communication or relationship links exist between insiders and traders.
As detection involves combining trading data with contextual information (i.e. employment roles, corporate relationships, or communication records), insider trading is one of the most complex typologies for surveillance teams to manage.
What These Typologies Reveal About Trade Surveillance
Mirror trading, wash trading, and insider trading differ mechanically, but share a common characteristic: none of them can be reliably detected by analysing isolated transactions. Instead, effective surveillance requires systems that can evaluate relationships between accounts, patterns across multiple trades, behaviour over time, and the broader context surrounding market events.
Silent Eight’s Trade Surveillance Agent evaluates complex trading alerts against internal surveillance policies and market abuse regulations, analysing behaviour across traders, instruments, and market conditions. Rather than focusing on a single transaction, it assesses patterns across related activity to determine whether behaviour may indicate market abuse.
Each alert produces a clear outcome: escalation, closure, or further review, supported by structured reasoning aligned with institutional policy and governance. Investigators can review these outcomes and apply their expertise to determine the appropriate next step.
Strengthening Surveillance Capabilities
Market abuse continues to evolve alongside changes in market structure and technology. Strengthening trade surveillance requires more than adding new rules or expanding alert libraries.
Effective detection increasingly depends on understanding how trading behaviour fits within the wider trading environment. This means connecting activity across venues, entities, and counterparties so investigators can see the full picture. It also requires analysing behavioural patterns across multiple transactions, linking alerts to related trading activity, participant relationships, and market events, and equipping analysts with technology that supports structured, consistent investigations.
Trade surveillance is not only about identifying anomalies in data. It is about determining whether those anomalies reflect behaviour that may indicate market abuse.
Contributor

Patrick Kirwin
Head of Product Management
Share article









